- ITMO University startup accelerator introduces Laeneco, a smart stethoscope
- Quantum communications: building 100% secure data transfer systems
The standard definition of Transaction state that “Every Query batch that runs in a SQL server is a Transaction.”, this means any query you run on a SQL server will be considered as a Transaction it could either be a simple SELECT query or any UPDATE or ALTER query.
If you run a query without mentioning the BEGIN TRAN keyword then it would be considered as an Implicit transition.
If you run a query which starts with BEGIN TRAN and ends with COMMIT or ROLLBACK then it would be considered as Explicit Transaction.
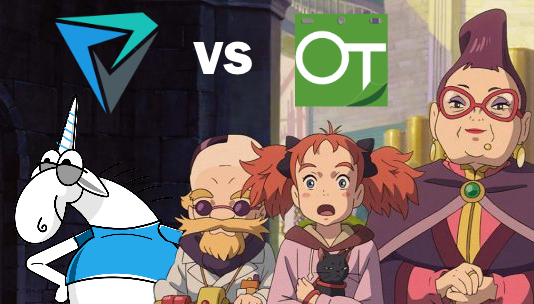
In this article, I will tell about my participation in the first (out of two so far) Telegram blockchain contest. I didn't win any prize. However, decided to combine and share the unique experience I have had from the start to finish line, so my observations could help anyone who is interested.
Since I didn't want to write some abstract code, instead make something useful. I created instant lottery smart-contract and website which shows smart-contract data directly from Telegram Open Network (TON) avoiding any middle storage layers.
The article will be particularly useful for those, who want to write their first smart-contract for TON but don't know where to start.
Using the lottery as an example, I will go from setting up the environment to publishing a smart contract, interacting with it. Moreover, I will create a website that will show smart-contract data.
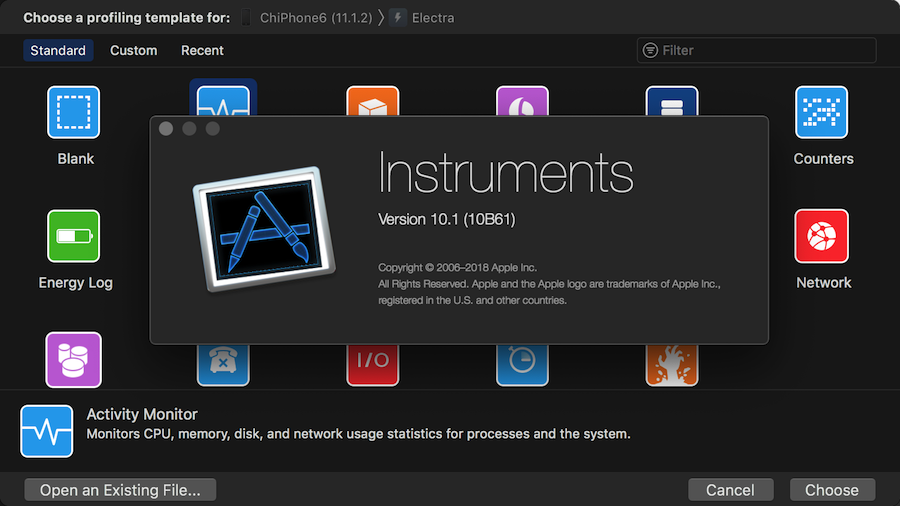
Instruments for Apple's Xcode is a tool for performance analysis of an iOS application. In 2018 Apple introduced Custom Instruments — an opportunity to expand the standard set of instruments for application profiling. When existing tools are not enough, you can create new ones yourself — it will collect, analyze and display the data the way you need.